Privacy Risks in Data Collection and Storage
Privacy Risks in Data Collection and Storage
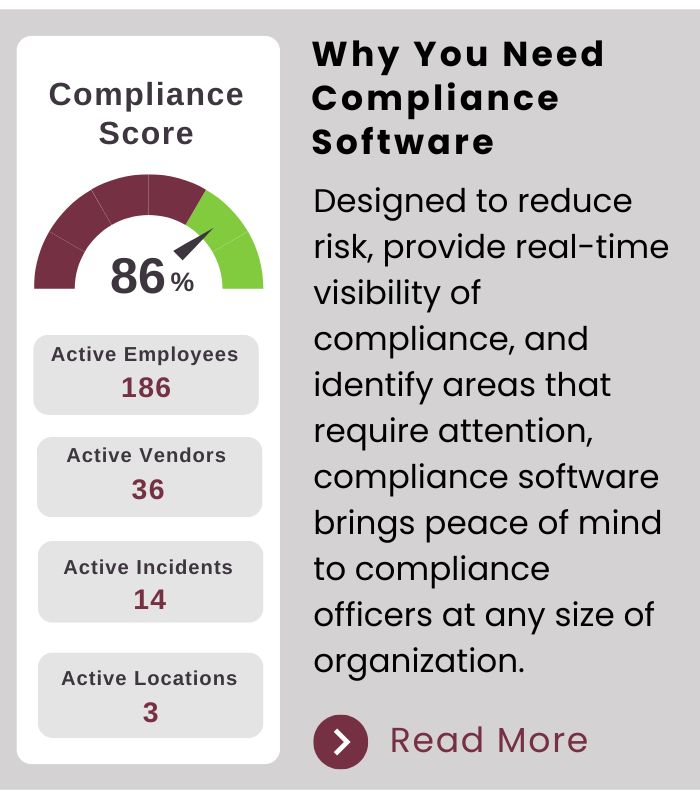
Organizations store vast amounts of personal information, ranging from user data to sensitive financial data. This creates significant risks, including unauthorized access, data breaches, and misuse by third parties. Many companies use encryption and secure storage methods, but vulnerabilities still exist due to cyberattacks and weak security policies.
For instance, major data breaches like the Facebook Cambridge Analytica scandal exposed millions of users' data, raising concerns about data privacy and corporate responsibility. Companies must comply with data protection laws, such as the GDPR, to make sure user information is safe.
Example: Equifax Data Breach (2017)
Misuse and Protection of Computing Resources
Computing resources can be misused in various ways, like malware infections, unauthorized software installations, and excessive resource consumption. Such uses can lead to slow system performance, network congestion, and security vulnerabilities.
Organizations implement strict IT policies, firewalls, and monitoring systems to prevent things like this from occurring. Regular security audits and employee training programs also help in mitigating risks associated with resource exploitation.
Example: Cryptojacking
Unauthorized Access to Information
Hackers will exploit vulnerabilities in systems to gain unauthorized access to sensitive data. They use techniques such as phishing, brute force attacks, and exploiting software to infiltrate networks. One of the most common attack vectors is weak or stolen passwords, which allow criminals to gain entry into private systems. Organizations mitigate these threats by using multi-factor authentication, intrusion systems, and constantly monitoring over the network. However, despite using these measures, cyberattacks continue to evolve, requiring constant advancements in cybersecurity.
A real world example of unauthorized access occurred during the 2021 Colonial Pipeline ransomware attack. Hackers used compromised credentials to infiltrate the company’s network, resulting in a temporary shutdown of fuel supplies along the U.S. East Coast. This incident showed the critical importance of a strong authentication protocol and the severe consequences of cybersecurity breaches. In response, companies worldwide have reinforced their security policies, emphasizing employee training and the adoption of zero trust security models.
Example: Colonial Pipeline Cyber Attack (2021)

Benefits and Risks of Computing Innovations
Innovations with computers have transformed industries, improving efficiency, accessibility, and communication. However, they also introduce risks such as job displacement, privacy concerns, and ethical dilemmas.
For example, AI enhances decision-making but can also have biases if not carefully managed. The automation of tasks has made work easier but has also led to layoffs for some people.
Example: Facial Recognition & Privacy Concerns
